成功したいですか? 目立ちたいですか? 当社の製品を選択してください。 数年間、優れたSC-300模擬試験教材を提供するように最善を尽くしています。 当社の製品を選択した場合は、試験を受験して有効な認定資格を取得し、Microsoft SC-300模擬試験教材で大きなメリットを得ることができます。 適切なポジションに応募する場合、Microsoft Identity and Access Administratorが役立ちます。 よろしければ、SC-300模擬テストファイルを使用して、新しい一歩を踏み出し、より良い未来を実現してください。
Microsoft SC-300認定試験は、Microsoft Azureでのアイデンティティとアクセスソリューションの管理と構成を担当するプロフェッショナルを対象としています。この認定試験は、クラウドおよびハイブリッド環境で安全なアクセスソリューションを設計および実装するために必要なスキルと知識を検証します。この試験は、Microsoft Azureアプリケーションおよびサービスのアイデンティティ、アクセス、ガバナンス、およびコンプライアンスを管理する候補者の能力をテストすることを目的としています。
Microsoft SC-300試験に合格した候補者は、Microsoft Certified:Identity and Access Administrator Associate認定を獲得します。この認定は、個人がMicrosoft Azureおよびその他のMicrosoft Cloud ServicesのIDソリューションを管理およびアクセスするために必要な知識とスキルを持っていることを示しています。この認定はグローバルに認識されており、アイデンティティおよびアクセス管理者、セキュリティエンジニア、セキュリティアナリストなどのさまざまな職務につながる可能性があります。
効果的-素晴らしいSC-300勉強方法試験-試験の準備方法SC-300模擬試験問題集
電子デバイスでの学習は、実際の研究に触れることに反します。 SC-300試験ダンプは、試験資料の世界有数のプロバイダーの1つとして知られていますが、その内容についてはまだ疑わしいかもしれません。したがって、特に今後の参考のためにいくつかのデモを提供し、それらのダウンロードに対して料金を請求しないことを約束します。その後、SC-300テストの質問を使用することが適切かどうかがわかります。明確な説明を提供するために回答と質問が用意されています。ダウンロードに問題がある場合は、必ずサービスにアクセスしてください。
MicrosoftのSC-300試験は、クラウド環境でユーザーのアイデンティティとアクセスを管理するIT専門家のスキルと知識をテストする厳密かつ包括的な認定試験です。この試験に合格することで、IT専門家はこの重要なIT分野での専門知識を証明し、アイデンティティとアクセス管理のキャリアアップを図ることができます。
Microsoft Identity and Access Administrator 認定 SC-300 試験問題 (Q128-Q133):
質問 # 128
You need to identify which roles to use for managing role assignments. The solution must meet the delegation requirements.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
正解:
解説: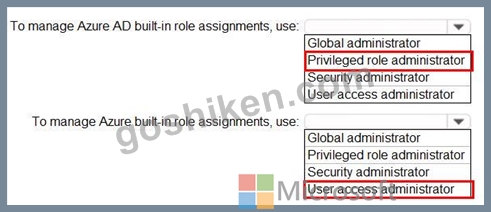
Reference:
https://docs.microsoft.com/en-us/azure/role-based-access-control/role-assignments-portal
https://docs.microsoft.com/en-us/azure/active-directory/roles/permissions-reference
質問 # 129
Your network contains an on-premises Active Directory domain named contoso.com. The domain contains the objects shown in the following table.
You install Azure AD Connect. You configure the Domain and OU filtering settings as shown in the Domain and OU Filtering exhibit. (Click the Domain and OU Filtering tab.)
You configure the Filter users and devices settings as shown in the Filter Users and Devices exhibit. (Click the Filter Users and Devices tab.)
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
正解:
解説:
Explanation
Graphical user interface, application Description automatically generated
Only direct members of Group1 are synced. Group2 will sync as it is a direct member of Group1 but the members of Group2 will not sync.
Reference:
https://docs.microsoft.com/en-us/azure/active-directory/hybrid/how-to-connect-install-custom
質問 # 130
You need to meet the authentication requirements for leaked credentials.
What should you do?
- A. Configure an authentication method policy in Azure AD.
- B. Enable federation with PingFederate in Azure AD Connect.
- C. Enable password hash synchronization in Azure AD Connect.
- D. Configure Azure AD Password Protection.
正解:C
解説:
Topic 1, Litware, Inc
Overview
Litware, Inc. is a pharmaceutical company that has a subsidiary named Fabrikam, Inc Litware has offices in Boston and Seattle, but has employees located across the United States. Employees connect remotely to either office by using a VPN connection.
Identity Environment
The network contains an Active Directory forest named litware.com that is linked to an Azure Active Directory (Azure AD) tenant named litware.com. Azure AD Connect uses pass-through authentication and has password hash synchronization disabled.
Litware.com contains a user named User1 who oversees all application development. Litware implements Azure AD Application Proxy.
Fabrikam has an Azure AD tenant named fabrikam.com. The users at Fabrikam access the resources in litware.com by using guest accounts in the litware.com tenant.
Cloud Environment
All the users at Litware have Microsoft 365 Enterprise E5 licenses. All the built-in anomaly detection polices in Microsoft Cloud App Security are enabled.
Litware has an Azure subscription associated to the litware.com Azure AD tenant. The subscription contains an Azure Sentinel instance that uses the Azure Active Directory connector and the Office 365 connector. Azure Sentinel currently collects the Azure AD sign-ins logs and audit logs.
On-premises Environment
The on-premises network contains the severs shown in the following table.
Both Litware offices connect directly to the internet. Both offices connect to virtual networks in the Azure subscription by using a site-to-site VPN connection. All on-premises domain controllers are prevented from accessing the internet.
Delegation Requirements
Litware identifies the following delegation requirements:
* Delegate the management of privileged roles by using Azure AD Privileged Identity Management (PIM).
* Prevent nonprivileged users from registering applications in the litware.com Azure AD tenant-
* Use custom catalogs and custom programs for Identity Governance.
* Ensure that User1 can create enterprise applications in Azure AD. Use the principle of least privilege.
Licensing Requirements
Litware recently added a custom user attribute named LWLicenses to the litware.com Active Directory forest. Litware wants to manage the assignment of Azure AD licenses by modifying the value of the LWLicenses attribute. Users who have the appropriate value for LWLicenses must be added automatically to Microsoft 365 group that he appropriate license assigned.
Management Requirement
Litware wants to create a group named LWGroup1 will contain all the Azure AD user accounts for Litware but exclude all the Azure AD guest accounts.
Authentication Requirements
Litware identifies the following authentication requirements:
* Implement multi-factor authentication (MFA) for all Litware users.
* Exempt users from using MFA to authenticate to Azure AD from the Boston office of Litware.
* Implement a banned password list for the litware.com forest.
* Enforce MFA when accessing on-premises applications.
* Automatically detect and remediate externally leaked credentials
Access Requirements
Litware wants to create a group named LWGroup1 that will contain all the Azure AD user accounts for Litware but exclude all the Azure AD guest accounts.
Monitoring Requirements
Litware wants to use the Fusion rule in Azure Sentinel to detect multi-staged that include a combination of suspicious Azure AD sign-ins followed by anomalous Microsoft Office 365 activity.
質問 # 131
You have a Microsoft 365 E5 subscription that contains three users named User1, User2, and User3.
You need to configure the users as shown in the following table.
Which portal should you use to configure each user? To answer, drag the appropriate portals to the correct users. Each portal may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
NOTE: Each correct selection is worth one point.
正解:
解説:
Explanation
Graphical user interface, text, application Description automatically generated
質問 # 132
You have an Azure AD tenant that contains the users shown in the following table.
You have the Azure AD Identity Protection policies shown in the following table.
You review the Risky users report and the Risky sign-ins report and perform actions for each user as shown in the following table.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
正解:
解説:
Explanation
質問 # 133
......
SC-300模擬試験問題集: https://www.goshiken.com/Microsoft/SC-300-mondaishu.html
- SC-300対応資料 ☀ SC-300試験時間 ? SC-300試験準備 ? 《 www.goshiken.com 》に移動し、“ SC-300 ”を検索して無料でダウンロードしてくださいSC-300トレーリングサンプル
- SC-300試験の準備方法|素晴らしいSC-300勉強方法試験|効率的なMicrosoft Identity and Access Administrator模擬試験問題集 ? ➽ SC-300 ?を無料でダウンロード☀ www.goshiken.com ️☀️で検索するだけSC-300最新テスト
- SC-300トレーリングサンプル ? SC-300最新テスト ? SC-300勉強方法 ? ✔ SC-300 ️✔️の試験問題は☀ www.goshiken.com ️☀️で無料配信中SC-300合格対策
- Microsoft SC-300勉強方法 - GoShiken - 認証の成功を保証, 簡単なトレーニング方法 ? ☀ www.goshiken.com ️☀️にて限定無料の「 SC-300 」問題集をダウンロードせよSC-300日本語試験情報
- SC-300復習教材 ? SC-300問題集 ? SC-300トレーリングサンプル ? 時間限定無料で使える【 SC-300 】の試験問題は「 www.goshiken.com 」サイトで検索SC-300試験準備
- 真実的-一番優秀なSC-300勉強方法試験-試験の準備方法SC-300模擬試験問題集 ? 今すぐ【 www.goshiken.com 】で▛ SC-300 ▟を検索して、無料でダウンロードしてくださいSC-300無料試験
- 認定するSC-300勉強方法 - 合格スムーズSC-300模擬試験問題集 | 最高のSC-300復習範囲 ? ( www.goshiken.com )を開いて☀ SC-300 ️☀️を検索し、試験資料を無料でダウンロードしてくださいSC-300勉強方法
- SC-300合格対策 ? SC-300ソフトウエア ? SC-300試験時間 ? ( www.goshiken.com )には無料の[ SC-300 ]問題集がありますSC-300認証資格
- 認定するSC-300勉強方法 - 合格スムーズSC-300模擬試験問題集 | 最高のSC-300復習範囲 ? 《 www.goshiken.com 》の無料ダウンロード[ SC-300 ]ページが開きますSC-300ソフトウエア
- SC-300実際試験の質問、SC-300模擬試験問題集 ? ➤ www.goshiken.com ⮘サイトにて「 SC-300 」問題集を無料で使おうSC-300トレーリングサンプル
- 認定するSC-300勉強方法 - 合格スムーズSC-300模擬試験問題集 | 最高のSC-300復習範囲 ? “ www.goshiken.com ”には無料の➡ SC-300 ️⬅️問題集がありますSC-300最新テスト